Learn from Industry Experts
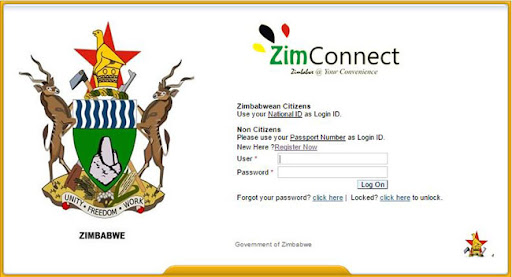
Best Internet Services. Providing world class services and the drivers behind total E-governance in Zimbabwe towards the attainment of vision 2030.
Vision
To offer world class internet services to Government of Zimbabwe through contemporary technologies.
Mission
To be the sole, efficient & affordable service provider in promoting Zimbabwe's
e-governance services.
Core Values
Patriotism, Innovation, Integrity, Team work, Commitment.
Our Most Popular Courses
Tailored for government ministries, departments and parastatals.
Our Story
We take pride in our capacity to back-up service delivery with aftersales support, guided by our mandate to be the sole Internet Service Provider to the Government of Zimbabwe.
G.I.S.P is mandated to provide fast, reliable, high tech value driven and cost effective back haul internet connectivity solutions to all Government Ministries, Departments and Parastatals.
est_1997
Be in Demand with Our Professional Training
Register your department emails under the .gov.zw domain for official government identification..
- Managing Top Level Domains (.gov)
- Domain Registration and Maintenance
- Web Hosting
- Web Content Management & Training
- Internet Connections
- Electronic Mailing (e-mail)
- User Support Services
- ICT Consultancy & Server Configuration
- The National Emblem of Zimbabwe/ Coat of Arms MUST be displayed on all Government websites.
- All Government websites should be identified by the name of the entity on the home page, e.g. ” Official website of the Office Of The President and Cabinet“.
- All Government websites MUST run on .gov.zw domains.
- All Ministries’ websites should be hyperlinked to the Government Web Portal “www.zim.gov.zw”.
- All Government websites should have a link to the Government email platform.
Get equipped with graphics design and content managements skills for you ministry/ department.
Number Speaks
27+
Ministries
35+
Departments
12+
Partners
150+
Professionals